Informatique
Avec l’évolution des débits de connexion et la digitalisation des applicatifs, les infrastructures hybrides ou cloud se développent pour vous offrir une flexibilité et une disponibilité plus complète qu’une infrastructure 100% physique. YES, we Cloud !
Le choix d’infrastructure parmi ces différentes philosophies de SI dépend essentiellement de 4 enjeux que nous déterminons avec vous :
> Disposez-vous en interne de la ressource informatique et de la compétence nécessaires ?
> Quelle disponibilité d’accès à votre infrastructure informatique est nécessaire pour couvrir vos enjeux business ?
> Quelle est la criticité d’un arrêt informatique dans votre chaine de production ?
> Quel est le niveau de confidentialité de vos données ?
Les données sont le socle essentiel de votre Système d’Informations, et vous allez déterminer l’ensemble de l’organisation du SI selon les choix techniques que vous effectuez. Koesio vous aide à évaluer vos enjeux et mettre en place l’infrastructure informatique la plus résiliente et évolutive.
Serveur et stockage
Nos partenariats forts avec les acteurs majeurs de l’IT, constructeurs et éditeurs, vous apportent une réponse parfaitement adaptée à vos enjeux d’infrastructures informatiques pérennes et performantes.
Sécurité de l'infrastructure
La sécurité est au centre de notre réflexion, et le PCA / PRA est un élément déterminant dans cette réflexion sur la protection de votre patrimoine numérique.
Interconnexion de sites
La mobilité et le télétravail étant devenus un usage, nous intégrons la réflexion de l’interconnexion de sites pour rendre votre infrastructure informatique toujours accessible depuis l’extérieur par vos collaborateurs.
Matériel et Périphériques connexes
Toutes les composantes de votre SI sont partie prenante de la sécurité de votre infrastructure informatique : infrastructures, réseau, firewall, licences logicielles, postes de travail, comportements utilisateurs, nous faisons le tour avec vous des évolutions à mener ensemble.
Le maintien en condition opérationnelle est destiné aux PME ne disposant pas de ressources internes suffisantes, ou souffrant de manque de compétences sur certaines technologies, et aux grandes entreprises pour la gestion d’une partie de leur Système d’information. Le système d’information est la colonne vertébrale de votre entreprise. Bien construit, maintenu et sécurisé, votre infrastructure informatique est le socle pour exploiter vos données en toute sécurité tout en répondant à la mobilité grandissante de vos collaborateurs.
L’objectif du maintien en condition opérationnelle est de garantir un fonctionnement permanent de votre infrastructure informatique et vous accompagner dans les évolutions à venir. Le MCO couvre l’intégralité de votre parc informatique en termes de maintenance curative et proactive (infrastructures, réseau, sécurité, et postes de travail).
Lorsque vous souscrivez un contrat de services managés traitant le MCO de votre SI, un interlocuteur unique vous est attribué. Il s’agit d’un Responsable Opérationnel de Compte (ROC), son rôle est d’être au centre de la relation entre vous et nous.
Il connaît votre informatique, votre organisation et vos besoins, et en interne chez Koesio il est informé de toutes les interventions qui vous concernent. Il est en charge du suivi, de la coordination et du contrôle des actions, ainsi que de la communication et du reporting de celles-ci.
Il est le garant de nos engagements et sait vous accompagner dans l’évolution de votre infrastructure informatique et anticiper les développements nécessaires, étant constamment en veille technologique.

Les systèmes (serveurs et dispositifs de stockage) de l’entreprise partagent l’information numérique entre vos utilisateurs et/ou vos sites. Ils permettent de centraliser l’administration, la maintenance et la sauvegarde des éléments qu’ils contiennent. Autant dire qu’il est essentiel de faire le bon choix !
Plusieurs aspects sont à prendre en compte :
> L’usage du dispositif
> Sa configuration
> Son format
> Son mode de virtualisation
> Sa gestion de sauvegarde envisagée
> Ses connexions avec l’interne (LAN) et l’externe (Wan, internet, MPLS …)
Autant de critères qui détermineront notre préconisation pour vous accompagner à bien définir votre choix de configurations pour votre infrastructure informatique. Partenaire multi-marques (Dell, HPE, Lenovo, …) labellisé par tous les grands acteurs de l’IT, seul votre besoin nous guidera.
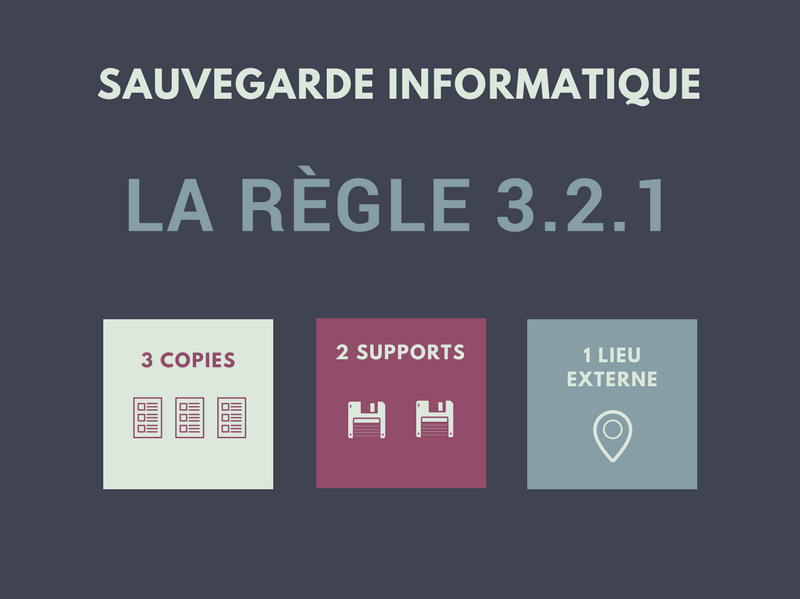
La donnée (Data) constitue le patrimoine numérique de votre organisation. C’est pourquoi les solutions de sécurité et de sauvegarde sont essentielles. Pour protéger votre SI et ses données, la bonne pratique s’appelle la « règle 3.2.1 ».
3 copies : La première partie de la règle consiste à s’assurer que les données sont conservées en 3 copies : 1 originale, 1 redondée et 1 sauvegarde dormante.
2 supports : afin de pallier un éventuel incident technique qui ne permettrait plus d’accéder au support, il est essentiel de permettre la réplication de la sauvegarde sur un support différent.
1 lieu externe : si le lieu de stockage est victime d’un sinistre, il est essentiel de disposer d’un second lieu de stockage, géographiquement distant.
Nos équipes vous accompagnent à déterminer et mettre en œuvre une politique de sauvegarde et de sécurité adaptée à votre infrastructure informatique.
Infrastructure Tier III ou Tier IV pour une sécurité maitrisée des données et de vos serveurs
Haute redondance pour une disponibilité optimale de vos applications métiers
Locaux sécurisés et composants redondés pour gérer les évènements impactants
Sauvegarde des données intégralement cryptée pour diminuer votre vulnérabilité

Face aux nombreuses attaques toujours plus complexes qui inondent internet, protégez votre réseau informatique. Ne choisissez plus entre sécurité et performance pour garantir la viabilité de votre réseau. Les contraintes fortes de sécurité et de disponibilité placent la sécurité de votre réseau au cœur de vos enjeux. Firewall, MPLS, interconnexion de sites, la mobilité et le télétravail vous imposent une gestion des accès pour garantir l’étanchéité de vos données sensibles.
L’infrastructure informatique a suivi l’évolution de « l’usage de l’outil ». C’est-à-dire que nous sommes passé d’un environnement « rigide et statique » (1 service = 1 serveur), à une infrastructure « portable, agile et redondée » grâce à l’avènement de la virtualisation. Nos Datacenters hautement sécurisés, et redondés vous garantissent un accès permanent à vos données. Vous bénéficiez d’une supervision de vos serveurs, de vos logiciels et de vos données avec une totale disponibilité 24h/24 et 7j/7.
5 caractéristiques principales
> une consommation & facturation à l’usage (pay as you go)
> un accès réseau ubiquitaire aux applications et aux données
> une économie d’échelle par la mutualisation des couches basses du SI
> une élasticité permanente et instantanée
> un service mesuré et contrôlé
4 modèles de service
> Infrastructure as a Service
> Software as a Service
> Platform as a Service
> Security as a Service
3 modèles de déploiement
> Public
> Privé
> Hybride

Abonnez-vous
à notre newsletter
Koesio, Entreprise de Services du Numérique (ESN), est le partenaire n°1 des PME et des collectivités pour leurs projets numériques.
Gestion & data
Infrastructure technique
Services managés
Supporte et centre de services
Financement
🚀 Préparé en seKret par l’agence web Marque Digitale
Laissez nous vos coordonnées ainsi que votre demande afin que nous puissions vous faire rappeler en moins de 24h ouvrées par le bon interlocuteur